Stay Ahead of Cyber Threats with St. Fox Managed Vulnerability and Patching Services
Proactively Identify Vulnerabilities and Apply Critical Patches to Minimize Risk.
95%
Patch Deployment Time
Critical patches applied within 24 hours.
85%
Vulnerability Reduction
Decrease in exploitable vulnerabilities in the first 30 days.
100%
Compliance Readiness
Audit-ready reports for GDPR, PCI-DSS, HIPAA, and more.
70%
Operational Efficiency
Reduction in manual patching workload.
Unpatched Vulnerabilities: The #1 Cause of Cyberattacks
60% of cyber breaches exploit known vulnerabilities that remain unpatched.
Manual patch management leads to delays, misconfigurations, and operational risks.
Organizations struggle to balance patching with operational continuity.
Proactive Vulnerability Management to Strengthen Your Security Posture
St. Fox provides comprehensive vulnerability and patch management to keep your systems secure and compliant.
Vulnerability Scanning
Regular scanning to detect weaknesses across all systems.
Patch Prioritization
Focus on critical patches based on threat intelligence and business context.
Automated Deployment
Streamlined updates to reduce manual effort and downtime.
Continuous Monitoring
Post-patch validation to ensure efficacy and compatibility.

Comprehensive
Vulnerability Scanning

Risk-Based Patch
Prioritization

Automated Patch
Management

Compliance-Ready
Reporting
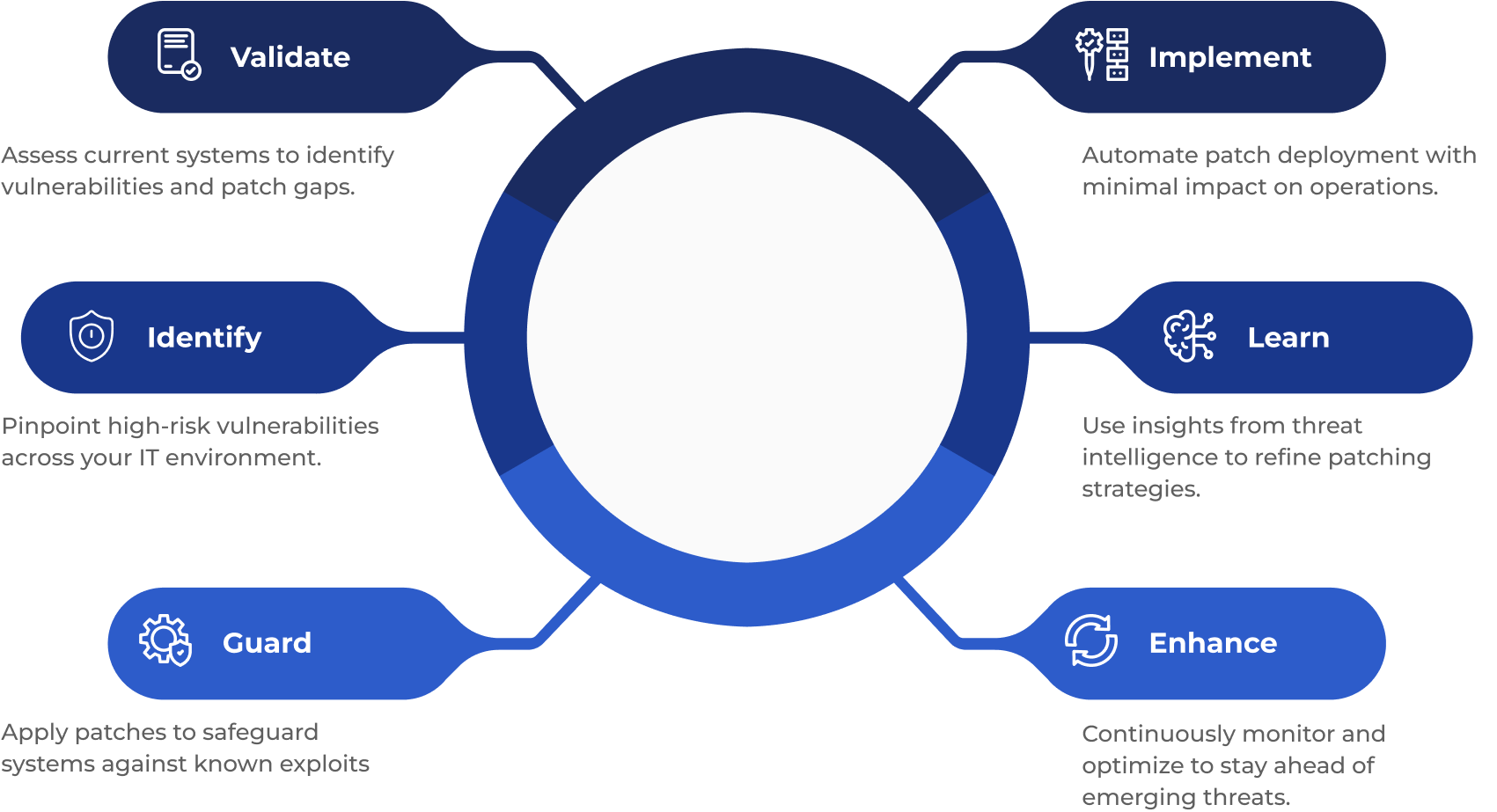
Strengthened by the VIGILE Framework
Access the Vulnerability and Patching Datasheet
Discover our approach, features, and benefits to secure your business.

Comprehensive Vulnerability Scanning
Detect and assess weaknesses across endpoints, servers, and cloud.
Compliance Reporting
Simplify audits with automated reports aligned with GDPR, PCI-DSS, and more.
Automated Patch Deployment
Ensure timely updates with minimal manual effort and downtime.
Risk-Based Patch Prioritization
Focus on the most critical vulnerabilities to reduce risk quickly.
Post-Patch Validation
Verify patch effectiveness and system stability.
Threat Intelligence Integration
Stay informed on vulnerabilities being actively exploited in the wild.
Proactive Vulnerability & Patch Management for Business Security
Identify and remediate vulnerabilities before attackers can exploit them.